Meet our dedicated team of technicians, your trusted allies in the ever-evolving digital landscape. Each one is committed to safeguarding your business, armed with the expertise and empathy to ensure your operations run smoothly. With us, you’re not just a client; you’re a partner. We’ve got your back, always.
Always On-Site
All Makes All Models
One Contract One Contact
Trusted Partner for Stretcher, Mattress & Hospital Bed Management

Your Bed Maintenance Partner
WHY EMERITUS
At Emeritus, we believe that hospital beds are the most critical medical devices in a healthcare setting. While others may overlook them, we love and care for hospital beds, recognizing their paramount importance. We are convinced there is a better way to provide hospital bed and stretcher maintenance services, one that prioritizes the needs of hospitals and their patients. Our innovative approach revolutionizes these services, making them more patient-centric and efficient. We strive to simplify hospital bed maintenance, ensuring it supports the hospital’s business goals and enhances overall operational efficiency. With Emeritus, you experience a seamless, effective maintenance program that keeps your equipment in top condition, ultimately improving patient care and satisfaction.

Your Bed Maintenance Partner
WHY EMERITUS
At Emeritus, we believe that hospital beds are the most critical medical devices in a healthcare setting. While others may overlook them, we love and care for hospital beds, recognizing their paramount importance. We are convinced there is a better way to provide hospital bed and stretcher maintenance services, one that prioritizes the needs of hospitals and their patients. Our innovative approach revolutionizes these services, making them more patient-centric and efficient. We strive to simplify hospital bed maintenance, ensuring it supports the hospital’s business goals and enhances overall operational efficiency. With Emeritus, you experience a seamless, effective maintenance program that keeps your equipment in top condition, ultimately improving patient care and satisfaction.

- Broken Beds Stacking Up In Hallways?
-

We understand the frustration of broken beds cluttering your hallways. Our Always On-Site Model ensures that our skilled technicians are always available to promptly address maintenance issues. With near-zero response time and the ability to service all makes and models, we keep your equipment in optimal condition, preventing the buildup of non-functional beds. Our proactive approach not only resolves immediate problems but also trains your staff to prevent future issues, ensuring your hallways remain clear and your equipment reliable.
- Are You Unable To Calculate Total Costs Of Bed Maintenance?
-

Tracking maintenance costs can be a challenge. Emeritus simplifies this with our comprehensive Bed Maintenance 2.0 program. Our detailed inventory and documentation system provides clear insights into every maintenance task and expense. With our cost-saving solutions, including potential savings of up to 30%, you can easily monitor and manage your budget. Our ‘One Contact, One Contract' approach streamlines the process, giving you a complete picture of your maintenance expenditures without the hassle of dealing with multiple vendors.
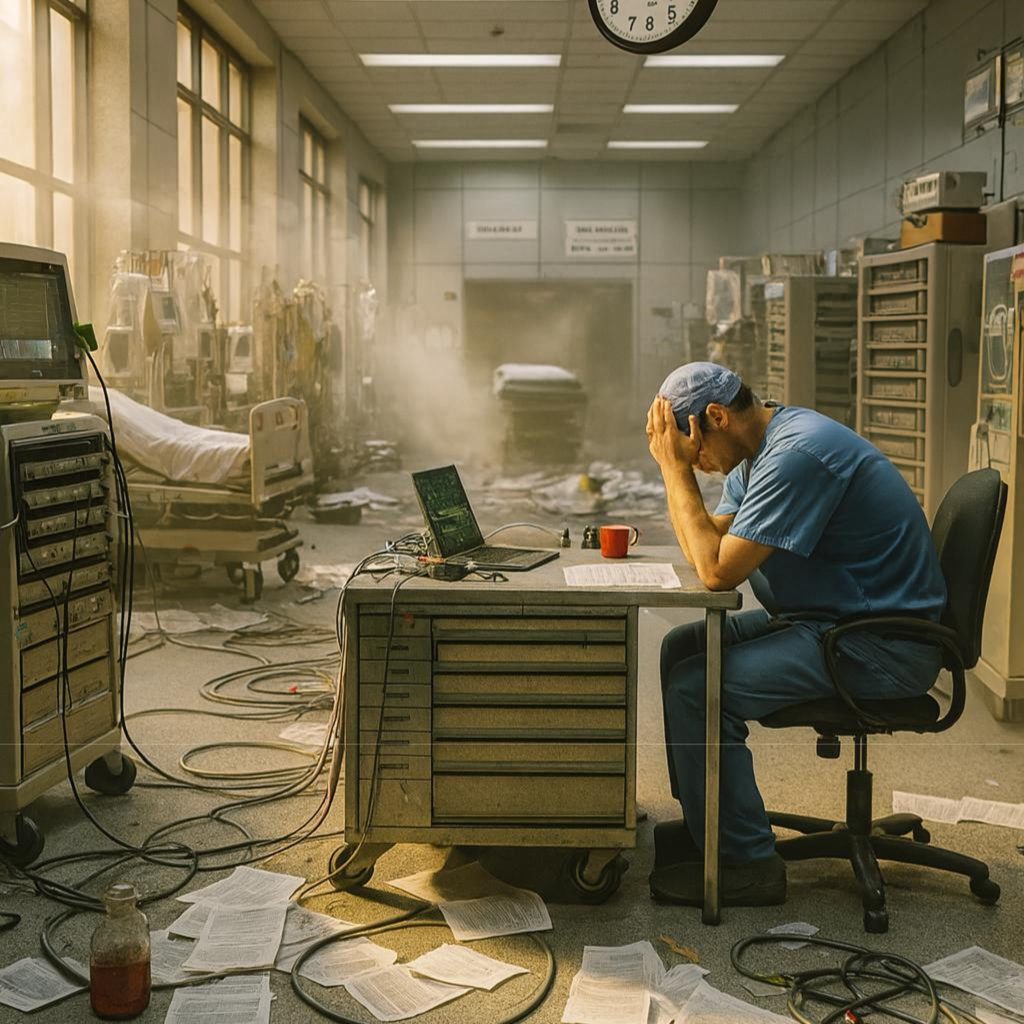
- Do Your Biomeds Hate Working On Beds?
-

We know that bed maintenance can be a tedious task for your Biomeds. Emeritus alleviates this burden with our Always On-Site Model, where our dedicated technicians handle all aspects of bed repair, medical equipment repair and maintenance. This allows your Biomeds to focus on more critical tasks, improving overall efficiency and job satisfaction. Our expertise in all makes and models ensures that every bed is maintained to the highest standards, reducing downtime and enhancing patient care.
- Tired Of Being Mistreated By Your Vendors?
-

Vendor issues can be a major pain point. At Emeritus, we prioritize building strong, high-communication relationships with our clients. No waiting around wondering when your beds will be serviced, when a technician will arrive, who will arrive, or when parts will be available. No biased service providers pushing you to replace your bed fleet rather than repair. No unnecessary module-level repairs. Our unbiased, in-house solution ensures that the hospital's goals and Emeritus’s goals are the same.
- Wasting Time Cutting Hundreds Of Pos?
-
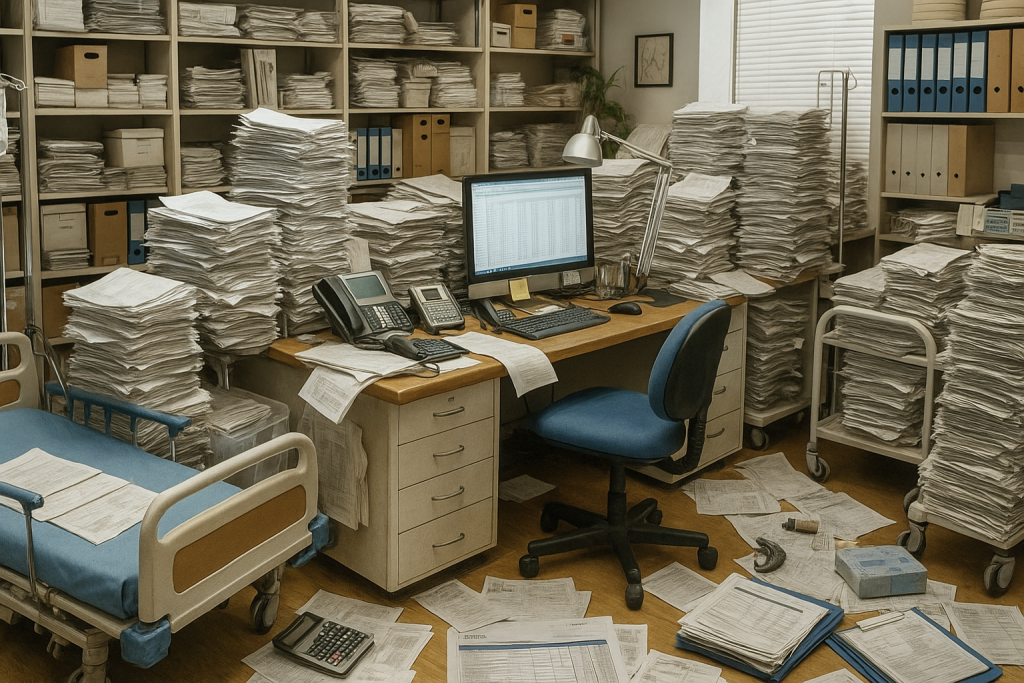
Cutting numerous POs and other administrative burdens associated with managing multiple time & material contracts is time-consuming and inefficient. Emeritus streamlines this process with our Power of One contracting and vendor agnostic service model. By consolidating all your maintenance needs into a single contract, we eliminate the need for multiple POs. This not only saves you time but also reduces administrative workload and ensures smoother operations. Our comprehensive inventory management system further simplifies the process to ensure documentation for all your beds and stretchers are available from a single vendor, allowing you to focus on providing quality patient care without the hassle of extensive paperwork.
- Struggling To Manage Hospital Bed Mattresses?
-

Managing hospital bed mattresses can be challenging. Emeritus offers a number of solutions to address these issues from annual audits, new launderable barrier technology, and mattress defect training. Our technicians not only maintain the beds but also ensure your mattresses are in top condition reducing risk for hospital acquired infections (HCI). We train your staff on proper mattress usage and identification of issues, preventing premature wear and ensuring patient comfort. Our proactive approach and near-zero response time mean that mattress problems are quickly addressed, reducing downtime and enhancing overall equipment reliability. With Emeritus, managing your hospital bed mattresses becomes a pain of the past.
Before partnering with Emeritus, the hospital endured the agony of delayed repairs due to excruciatingly long OEM wait times, suffered through prolonged downtime with agonizingly slow response times, and felt the sting of exorbitant maintenance costs without any relief or savings. Their struggles were intensified by their limited expertise in handling varied equipment, the painstaking task of manual inventory and documentation, and the sheer frustration of dealing with complex contracts.

With Emeritus, staff experienced a turnaround of joy and relief. The hospital now has always-on-site techs ready for immediate assistance. The near-zero response time brought swift resolutions, ensuring minimal disruption to their operations. They rejoiced in the up to 30% savings on maintenance costs and the assurance that all their equipment, regardless of make or model, was expertly supported. With automated inventory and documentation, their workload lightened, and simplified contracts streamlined their processes. Emeritus became their single point of contact, making their interactions effortless and their experience truly joyful.
"We appreciate how responsive the team is. The technicians are great to work with and collaborate well with our staff. The service is self-sufficient, ensuring everything is working smoothly and taking a significant load off our shoulders."
Robert
"Our technician is fantastic! He's sweet, easy to work with, and very responsive. Overall, the customer service is excellent, and we are very satisfied with the service provided."
Mark
"The overall experience has been great. Our dedicated in-house tech, in particular, is very responsive and ensures we stay informed. The company's approach to business is impressive, and we highly value their service."
Edward
"Communication is top-notch, and repairs are excellent. The team consistently keeps us informed and responds promptly to any inquiries. Their professionalism and dedication ensure that our equipment is always in optimal condition. The quality of their repairs is outstanding, and we've experienced significant improvements in efficiency and performance since working with them. We couldn't be happier with the service they provide."
Anthony
"The support team is remarkably responsive and attentive, promptly addressing any concerns or questions we have. Their efficiency and dedication ensure our operations run smoothly and without disruptions. The service level is consistently excellent, and we greatly appreciate their commitment to maintaining such high standards."
Paul
"We love that they work on all makes and models of hospital beds and stretchers. This flexibility is invaluable, as it means we can rely on them for any equipment we have, regardless of the manufacturer. Their expertise across various brands ensures that all our equipment is maintained and repaired to the highest standards. This comprehensive service has made a significant positive impact on our operations."
James
"They truly relieve the stress for our hospital facility managers. Knowing that we can depend on them to handle all our maintenance and repair needs allows us to focus on other critical aspects of our job. Their prompt and professional service means we never have to worry about equipment downtime. This peace of mind is invaluable, and their reliability has made managing our facility so much easier."
Michael
POSTED BY
antops
POSTED BY
antops
The team at Emeritus is ready to bring decades of experience to your organization. Reach out today and discover what a proactive technology partner can do for you.